Phishing Email Scams With Real Phishing Examples 2019
Phishing emails & phishing scams are dangerous. Phishing emails are hard to spot, look real, and can have devastating consequences. In this post we’ll look at real phishing examples, how to report phishing emails, and how to deal with phishing scams.
Phishing Email Scams Summary:
- A phishing email could look real
- We look at some phishing examples
- Anything can be faked, from sender name to signature
- There are some basic checks you should do
- 5 key things to be aware of
- The one secret to stopping phishing emails
What Are Phishing Emails and Phishing Scams?
Phishing emails are emails that pretend to be from a person or company, but are in fact fake. In business, a phishing email could come in from a regular supplier, informing you they’ve changed their banking details. Your company makes the payment, but the money never reaches your real suppliers, and is stolen in the phishing scam.
Another classic example is a phishing email from Netflix that says “Your account has been suspended”. It asks you to click a link and give your details to reactivate your account. The attackers then harvest those details and either use them to commit fraud, or sell them on the dark web.
Spam emails, as opposed to phishing emails, could be from a legitimate person or company, and are irritating but not necessarily malicious.
Why is phishing so dangerous? Phishing emails and phishing scams account for over 90% of all attacks online, from ransomware to malware, and password theft to data breaches.

A common misconception is that antivirus protects users from phishing emails. Unfortunately, this is not true.
Phishing Examples
Here are some real phishing examples that we at Retruster have caught in 2019:

This phishing example looks exactly like a legitimate message from Fedex. It's not, and clicking the link leads to a malicious website.
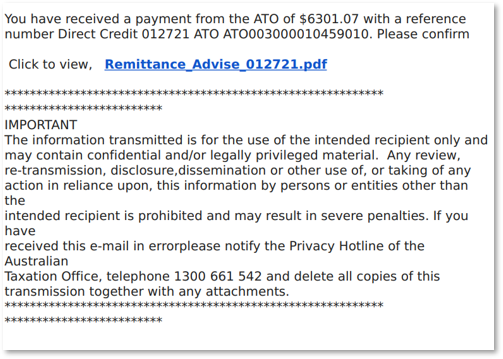
In this phishing example, the phishing scam gets the recipient excited that they have received money. It's fake of course, and clicking the link leads to the installation of malware on the recipient's system.
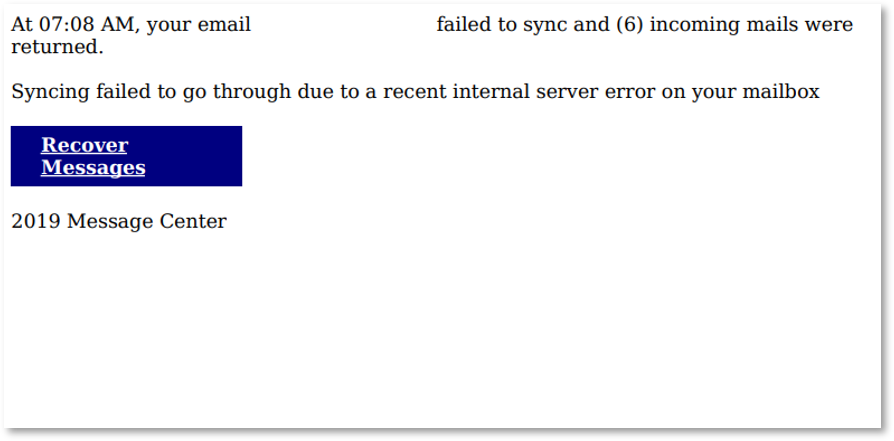
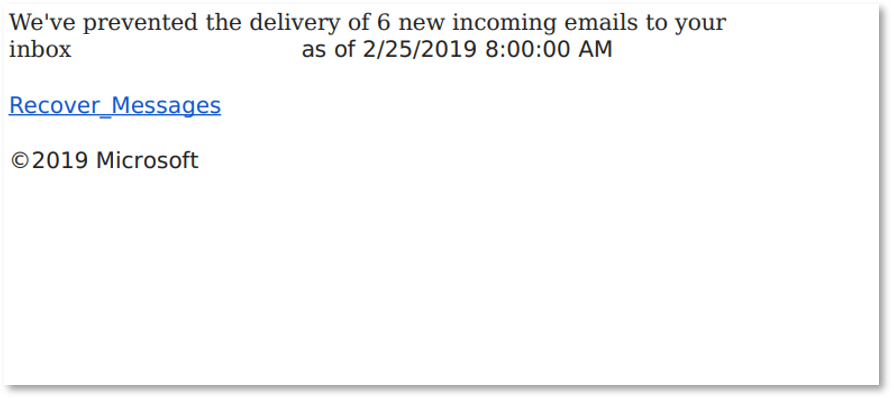
We took out the email address in this phishing email, but it was personally addressed, and the phishing scam makes the recipient think they are not receiving emails.
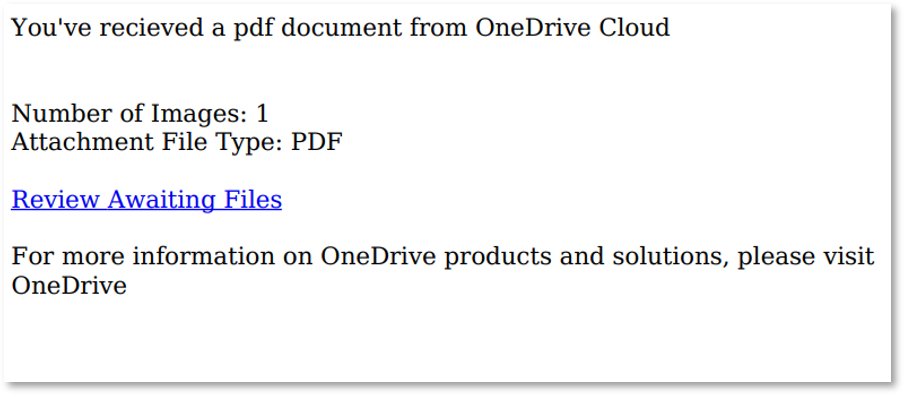
Great! Someone has sent you a PDF. What could it be? This phshing example shows that behind a link or button could be anything. A phishing scam is well disguised and plays on curiosity.
In this phishing example, you can see how fraudsters use real terms and logo's (which we removed in this case) to perpetrate their phishing scam.
Famous Phishing Email Examples
- 1. The Email That Changed America — Would You Have Fallen For It?
- 2. Phishing and Email Fraud Statistics 2019
- 3. Protect Those You Care About
- 4. CEO gets wings clipped after losing £39m in classic email scam
- 5. Target data breach
Phishing Example and Awareness In Combating Phishing
The first step in how to stop phishing emails is awareness. You, and the people you work with, have to be as cautious and vigilant online, as you would be outside in the street.
Just like if someone came up to you and offered something too good to be true, or you received a phone call to update your bank password, so too when it comes to online behavior you need to stay alert.
The second part of how to stop phishing emails is understanding – and unfortunately too many people are unaware of this – just how easy it is to send fake, or fraudulent emails. “Apple.com” might be a registered address, but what about the phishing example “apple-overdue-payments.com”? Or “.co”?
These manage to look legitimate, especially if we’re not specifically looking out for them. People even fall for “apple-payments@gmail.com” phishing emails, which may sound silly but again, if you’re not specifically looking out for it, the human eye can just pass over this information. Unfortunately, fraudsters can even, relatively easily, send you emails from real-looking addresses. So next time you get an email from “payments@amazon.com”, there is a chance that it’s not the real thing.
The issue of awareness has really come to the fore lately, with Google publishing warnings and their very own phishing quiz. There are a number of companies and websites that help when it comes to awareness and phishing examples, especially for your employees. These include the likes of the Anti-Phishing Working Group, and our very own Retruster.
Awareness of phishing emails, training and simulation are great first steps, but they only tackle a part of the problem – and sometimes leave you and your organization even more vulnerable than before.
The Latest in Phishing Emails and More Phishing Examples
Take a look at some of the latest research, findings and articles on phishing and fraud:
- 1. Phishing realization – We've all had this moment
- 2. Protect Those You Care About
- 3. Phishing, and Jeff Bezos’ Regret Minimization Framework
- 4. The Email That Changed America — Would You Have Fallen For It?
- 5. We’re All Sitting On An Asset We’re Not Using
- 6. Your Employees Need To Be Aware Of These 5 Online Fraud Tactics with Phishing Example
- 7. How To Stop Phishing Emails
- 8. What Is The True Cost Of A Phishing Email Attack?
- 9. Stop Phishing Emails With Microsoft 365
Phishing Emails and Phishing Scam Reading
Keep up with the latest talks and happenings in the phishing and email fraud space.
Netflix phishing scam targeting Aussies via dodgy emails
"The campaign has been targeting Netflix users across Australia, with users reporting having been sent a phishing email from an address posing as the legitimate support team for the streaming service, with styling and a logo that matches a typical Netflix communication."
Google wants to quiz you on phishing emails
"Google’s Jigsaw unit published a quiz that tests users’ abilities to identify phishing emails. The quiz tests you on a series of emails to see if you can distinguish telltale signs of phishing."
In Fighting Phishing Emails, Hyper-Vigilance Is Hyper-Costly
"Because phishing remains a top attack vector, it deservedly gets a lot of attention. What gets very little attention, however, is the cost of investigating legitimate emails that people mistake for threats."
Retruster Blogs on Phishing Emails With More Phishing Examples
Check out our top-read blog posts on phishing emails, phishing examples, and how to protect yourself
Stop Phishing Emails With Microsoft 365

Microsoft Office 365 offers some powerful features to stop phishing emails. We'll explore these tools and look at other alternatives to prevent phishing for your organization.
Choosing The Best Anti-Phishing Software in 2019

Anti phishing software has become critical for businesses in 2019. Phishing has become a serious threat to companies and consumers alike, and without anti phishing software, we are left completely vulnerable. We’ll look at what your options are when it comes to choosing the best anti phishing software in 2019.
What's the cost of a phishing email?

How much do you think a phishing email will cost your business? These emails are getting more sophisticated, their targeting is getting better, and you'll be shocked to discover how much a breach will cost your organization.
How to stop phishing

If you’re reading this, you’ve likely been the target of a phishing attack and are looking to protect yourself and those around you. If it hasn’t hit you yet, it will soon, along with others that you care about.
Your Employees Need To Be Aware Of These 5 Online Fraud Tactics

Share these latest tactics with your team to ensure you don’t fall victim to the latest in fraudulent online scams.
We all have a side to us that’s naturally curious, especially when it comes to finding out that a document is waiting for us, and that all we need to do is click to open it. Is it important? Could it be interesting?
Phishing and Email Fraud Statistics 2019

Phishing and email attacks are not only increasing as time goes on and our lives and data get stored online, but they’re evolving. Understand how Phishing and Email Fraud are repeatedly affecting executives and companies worldwide and how you can protect yourself.
We’re All Sitting On An Asset We’re Not Using

There are very few things worse than the feeling of a missed opportunity.
First, losing hurts. Daniel Kahneman and Amos Tversky Nobel Prize winners and trailblazers in the world of behavioral economics, first identified this “loss aversion”. We’d rather not lose $5, than find $5.
Second, we are programmed to hate losing out. “FOMO” has even been added to the Oxford Dictionary.
The Email That Changed America — Would You Have Fallen For It?

It was a single email that quite possibly changed the course of history. It was a single email that was used to gain access to thousands of Hillary Clinton and DNC emails. A scandal that is blamed for derailing her campaign, and accelerating Donald Trump’s climb towards becoming the 45th President of the United States.
Phishing, and Jeff Bezos’ Regret Minimization Framework

Made famous by one of today’s most successful leaders, Jeff Bezos, the Regret Minimization Framework is hot and trending. Celebrities are talking about it, sharing it on social media, and pushing others to adopt the mindset in order to stay motivated and achieve their goals. What many don’t realize, is that the framework plays a big role in combating phishing attacks and keeping yourself, your data, your money, and personal life secure.
Protect Those You Care About

It first came to our attention with the tragic story of Steve and Claudia Tatevich, an elderly couple from Minnesota who decided to buy a townhouse with their retirement savings, to move closer to their kids & grandkids.